Consider this; your company has recently decided to move on from paper documents to databases and spreadsheets. Most of the information you now interact with is in digital form and stored on your local computers. Your company has also connected your computers at the premises to the internet to ensure that you have access to information whenever you need it. The internet is proving to be quite useful for your business as you can now send and receive emails. In general, many improvements have been brought about by the transition to digital systems for your business, and you feel that this is a step in the right direction.
Unfortunately, even before you can start benefiting from the transition to digital systems, your systems are infected by an unknown and weird malware that has been eating into your database files, spreadsheets and making everything unusable. The files have been corrupted, and you cannot read anything. This means that all your documents are gone, and the malware has been modifying everything on your computers, from the files stored on them to the very core of the operating systems. The operating system has been getting modified and even logging into the systems is impossible.
You had no backups of the information. The only recent backup and accurate record for your business are the paper records you had shelved away, hoping that moving to the digital world will be a welcome way to get rid of paper. The replacement of the information management systems has not augured well for your business, and you have ended up losing a lot of precious information. So, you ask yourself, what has caused all that loss of information? Were you in part responsible for the loss of information, and can the information be recovered?
Cybersecurity
Information is a precious asset for many businesses and must be treated as such. With modern information systems, information is turned into valuable insight that drives a business and sustains it. Information for modern businesses, companies, and organizations has made it possible to provide more value to customers. With information, companies can be able to make better decisions and steps towards improving their operations. The use of timely information makes it possible for any business to make better decisions and steer itself away from losses and other perils waiting for the business.
Hackers
Whenever information systems are not kept safe while they are in digital form, they become shiny targets for hackers and other information criminals. If you have not enforced password use on your computers at the business premises, anyone can sneak in during the break and steal files by copying them onto a flash drive.

Additionally, poor password habits can mean that employees fired will come back to the company and use the same passwords to access your information systems. When they do, they will often cause changes and damages to your information in revenge for getting fired. These are risks that you would not have foreseen, but they are always known to happen. Many companies have been brought down by disgruntled employees who destroyed entire databases due to not being happy about how they were being treated at the company.
Modern information systems and computers at the office are also connected to the internet. A working internet connection is required for various office and business functions like communication, sharing files, and collaboration with peers and business partners.
Without proper network security measures such as firewalls and network rules, it is possible that an attacker from outside can penetrate your network and take over a computer that is connected to the internet. Connecting to the internet without safety precautions can expose your business or company to many threats from outside. It will make your business an open target for hackers and script kids who will want to try out their hacking skills and exploits they have been preparing.
Cybersecurity encompasses the attacks that are possible on your networked systems, the methods that hackers and attackers use to take advantage of weak security systems, as well as defense mechanisms and policies that can be used to ensure that your information system is kept safe and secure.
Knowledge of cybersecurity makes you aware of the security dangers lurking around your information systems and measures to ensure that your information is safe. The internet is not full of surfers and innocent engineers working to ensure that your systems share data at the speed of light. Some hackers work day and night to thwart the efforts of the engineers.
Hackers are computer criminals who use their knowledge of computer systems to gain unauthorized or illegal access to information systems. They know how to use computers and understand computer concepts such as networking, firewalls, and the operating system kernel. They are good at finding weaknesses in networks and computer systems and are always working to reveal new exploits and weaknesses in computer systems. The hackers are known to create their tools, but new hackers and script kids will purchase computer programs from the dark web to gain illegal access to information systems.
Computer hackers will always develop a countermeasure for each security measure that you enforce on your information system. They will try to work around every security update that you install on your system. Hackers also work day and night to create programs that will make their hacking faster and much easier. They will work on rootkits and password cracking software to use once they have found a way into your network.
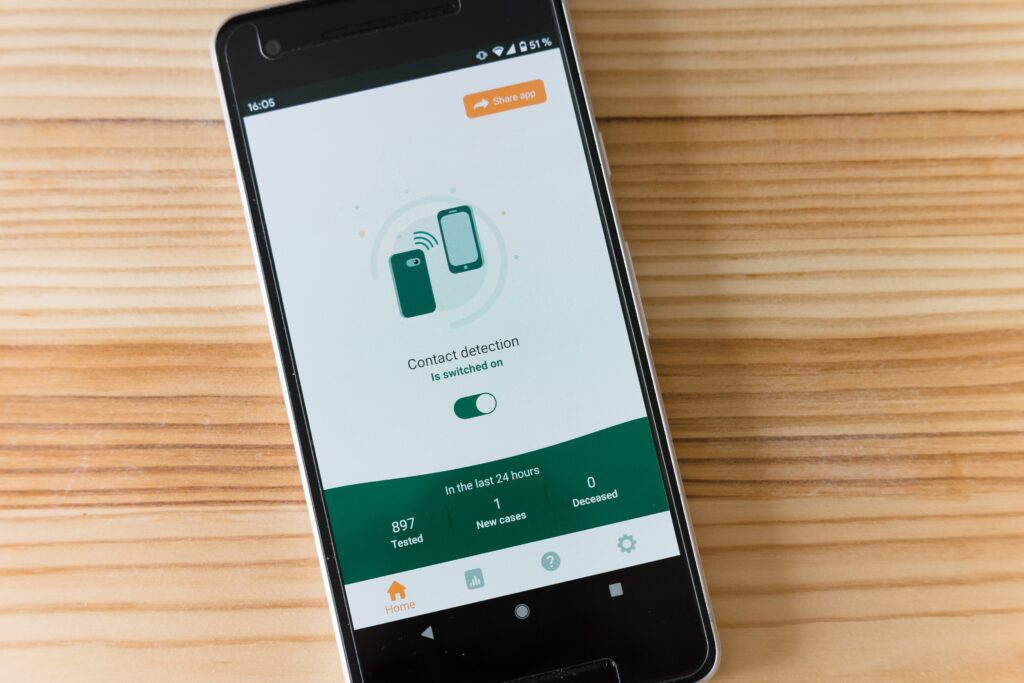
Hackers hack all kinds of devices from cars, thermostats, network routers, switches, computers, wireless devices, and even smartphones. When your security measures are not strong enough, the hackers will always try to find a way into the network, and once they are inside, it becomes very hard to detect what they are doing. It will be too late to tell that you are leaking information from your computer systems as computer hackers are known to work in silence.
If firewalls do not secure your computers, and there are no means of alerting you to what is going on, you will not be able to detect a hacking attack in progress.
Importance of Cybersecurity
Cybersecurity is all about knowing that hackers exist and their methods are getting sharper and cruder by the day. With the growth in computing power, the hackers’ methods to break into systems are getting worse. Hackers are also known to cripple information systems to make a statement and prove how well they can use their time. Well, the hackers are always working to ensure that you are unable to make use of that surge in demand on your online store or e-commerce store.
The crippling attacks that hackers make on huge establishments on the internet are meant to disrupt the business flow and destabilize the economy. Hackers can be hired by anyone that needs to cause some disturbance or demonstration on the internet. As long as you have a means of getting in touch with a good hacker with a credible reputation with several records under their knuckles, you will be able to target that convenience store that has not been treating you very well.
When you are aware of the threat presented by hackers to your companies and business, you will also be more aware that hackers can strike at any time. As such, you will be more prepared for their attacks and put measures that will alert you that there is a worm crawling through your information system in search of weaknesses in your information system.
Security measures such as honeypots are used to catch the hackers by presenting a “fake” security system to them. The hacker will think that the honeypot is the actual system and immediately dive into the information system. However, the honeypot is intended to keep the hacker engaged long enough to reverse their hacks, infect the systems they are hacking you from, and even start tracing their IP.
Hackers are known to cloak many of their moves by hacking from hidden IP addresses and virtual machines. This makes their steps very hidden, and most of the time, it is almost impossible to tell when a hacker has been visiting your system. The hacker will try to attack your system by using other computer systems to make the connection.
The hacker will also try to reroute their connections several times around the globe before striking out. As such, your security measures must be able to detect suspicious connections fast enough to stem the leak or loss of information from your computer systems and applications.
Hackers are dangerous elements that [resent an ever-present threat to your information. They can cause damage to your data, modify it or delete your entire trove of information. When they have access to your systems, they can even install back doors and other strange applications on your systems to ensure that they can SSH to your computer whenever you are not busy on it.
Using the spare time that the computer is left on, the hacker will upload all the data on your local storage to a cloud server or computer. The theft of information is very risky, and many huge companies have been known to run into billions of losses due to their confidential information getting stolen.
Private and Confidential Information
Consider a bank that holds your money. If the bank has been hacked, your private records might get stolen and sold by the hackers on the dark web market to other criminals. The other criminals will use the private information known to only you and the bank to carry out social engineering attacks.
These are part of cybersecurity and tend to hack into the very nature of human beings, such as trusting names and people in authority. Hackers are using the trust that humans have established between themselves over the ages to steal information and cause them to take actions they would have otherwise suspected from the very sniff of it.
Social engineers are very friendly con artists who will be full of answers and try to use perceived relationships to steal information from you. For instance, they might use your relationship with the bank to cause you to change your password for online banking. When you do this, they will be able to log into your bank online and transfer funds to their accounts. However, social engineering is not always successful as we are always suspicious of the people around us.
The human race has evolved socially to treat every unknown phone call as a scammer promising a huge part of their so-called inheritance to get part of the transfer fees. We receive so many texts claiming that we have won in a competition that we did not complete even to give these messages a second look.
Unluckily, social engineering attacks are very lethal when they are successful. Once the hacker has gained the trust of the unsuspecting banking customer, they will take advantage of this to make away with all their information and steal all their money from them.
Social engineering is also used when hacking into systems to cause people to reveal their passwords or change some system configurations, which will make it easier for the hackers to gain access to the systems. The hacker might call in as technical support, asking for certain IP addresses to be allowed into the network for remote administration.
These are all tricks that are used to break into information systems. Once the hacker has a nail-hold of your information system, they will rip away the entire facade of security and protective measures with their attack.
Hacking attacks are quick and lethal. They borrow this because they are planned for well in advance, and the hacker tries to understand the system inside and out before they can carry out the attack. Your information will be at the mercy of the hacker when you do not take measures to ensure that your information is safe.
Modern computer users are required to use strong passwords and ensure that the passwords they come up with are not once that easy to guess up. The password you use should not include simple names such as admin since these are commonly used in breaking into information systems.
Brute force attacks, for instance, are heavily used to guess the passwords to enter into information systems. The systems will ask for a password, and the hacker will use the brute force applications to guess as many combinations of letters, numbers, and symbols as they can to the system. Some of the systems will lock out further attempts.
Still, if you have not enforced this security measure in your information system, the brute force attack will go on and on for a long time. Eventually, the brute force software will be able to create the correct combination of letters and numbers that make up your password. The hacker always has an arsenal full of tools in their toolkit.
They will use all the tools at their disposal to try and break into your systems. Unless you have secured your information systems, there will be no way that you will be able to prevent your computers from being digitally broken into and the information that you have stored on them getting stolen.
Cybersecurity is an important concept to learn, especially in an uncertain digital future where our information is at the mercy of the most lethal hacker. With the advances in computing power, most of the security measures we put in place for our information can easily be broken.
Computer power combined to create password and decryption key sequences for information means that hackers now take less time to enter information systems. Securing your information systems means protecting the networks that you are on and securing your computer.
Secure networks are important for modern computer systems, and the office should be able to filter all incoming and outgoing traffic on their networks. Before requests can get to the internet, you must obfuscate the IP address of the senders. This will ensure that your network’s internal network design and arrangement are not revealed to the outside world.
When you do not know such information for your network, it will be very difficult for hackers to understand how your system has been designed. They will be unable to break into your networked systems when your network has been designed to be very hard to break into.
Firewalls ensure that all kinds of IP addresses cannot access your networks. The firewall will filter all the incoming traffic on your network, and it will also ensure that the suspicious traffic is blocked. The use of network security measures also ensures that hackers cannot send harmful files to the computers on the network.
The use of sub-nets that hide the real identity of the computers used to send and receive information means that hackers will not accurately target an information system on your network. They will have a very hard time breaking into your computer networks, and hacking the computers themselves will be even much harder.
With cybersecurity knowledge, you will be more aware of the threats lurking around your network and how best to protect yourself. The computers you use should have measures to ensure that hackers are unable to break in and alert you whenever there is suspicious activity. Additionally, you should notice early signs of hacking in progress and take steps to ensure that your system incurs no further damage.
Modern businesses and organizations need to be aware of cybersecurity and what role it has to play in the security of their information. Modern information systems are known to deal with very sensitive information. Whenever these systems are protected from the efforts and attempts of hackers, your customers are more confident in your business.
Modern information systems are used in various aspects of running a business or an organization. When you know the dangers that your systems can be exposed to when they are not well secured, you will secure your systems better.
Securing your information systems is more important than anything else and the reason you should work to ensure that you have better cybersecurity strategies for your business. Any modern business is a likely target for hackers and other information criminals who intend to ensure that they cripple systems and cause them not to render the services they should be delivered to customers.
Crippling Hacks
For instance, modern e-commerce businesses and companies are known to handle millions of requests each second. Whenever a hacker does not want the company to operate at its peak ability, it will initiate a denial of service attack. A denial of service attack is one of the attacks known to be sued to cripple the ability of companies and businesses to handle genuine and legitimate business.
Whenever they are carried out on a business, the business is overwhelmed by incoming requests for information that it forgets to handle the requests from the legitimate customers. The service outage will affect business for the company, and it will be unable to handle its customers.
Denial of service attacks overwhelms a business’s computer systems and ensures that it cannot render services to its customers. The customers will be unable to conduct any business on the platforms owned by the company for the duration of the attack.
Even though the denial of service does not steal any information, it is still a deadly cyber-attack and must be treated with a level of seriousness. The information system owners must have measures of countering the denial of service attack or at least recover pretty quickly from the same attack.
These attacks can even get more serious and deadly when they are carried out from a fleet of computers that have been hacked into by the hacker and used as command centers for the hacker. In this case, it gets to be known as a distributed denial-of-service attack.
The distributed denial of service attack makes use of a lot of slave computers that have been controlled by the hacker and are used to carry out some of the most lethal denials of service attacks known in modern computer science. The distributed denial of service attacks is intended for the business giants with many orders to process and stronger computing infrastructure.
Hackers make use of the unprotected nature of many modern information systems to steal information, install their worms and rootkits in addition to causing damage to information. The hackers usually intend to gain valuable information, but others will hack into information systems for the sheer pleasure of hacking.
The hacker will practice less secure systems to gather a rap and be more confident when attempting to hack into well-secured systems. The hackers will always come up with new means and ways of breaking into systems. When you have beaten them at one kind of attack by raising your shields in time, they will develop better digital weapons that they will use in retaliatory attacks to break past all your defenses and steal your information.
Understanding the hacker’s mindset is very important to understand them and the means they will use to break into your information systems. The hackers will always try to attack your system using certain styles, which usually form their digital traces.
When the hacker programs in a certain style, it will be possible to build up their profile whenever they hack into an information system. Hackers are motivated by various things, and there are many reasons they are known to hack into information systems. Most of them are usually curious about how your system has been configured, while others will simply be looking for a challenge that their latest hacking script can beat.
Hacker Awareness
Be ready for hackers at all times, and by being at the ready, you will be able to counter all the scripts and suspicious traffic coming your way from the hackers. The hackers are always looking for ways to break into secured systems, and whenever you regularly update your applications, you will be able to keep them at bay.
Hackers will not have to bother you when you have security mechanisms to ensure that your systems are never hacked from the outside and inside. The policies you put in place for securing your information systems will ensure that the hacking incidences are taken care of. Any leakage or point of weakness in your system security will be properly handled. The hackers will not break into your information systems if they cannot get to the employees. When one of the hacker’s plan components is not working, their entire plan will be a house of cards, useless and ineffective.
When you have an understanding of the issues that surround cybersecurity, your information will be more secure. It will be possible for you to conduct business without worrying about your data and private information getting leaked to the dark corners of the web. Cybersecurity is all about being ready and aware of the threats that are all around you.
It encompasses infrastructure changes and upgrades, employee policies, and other measures that will ensure that your information can survive the brute attacks that hackers mete out. The hackers will have a harder time breaking into systems considered the hackers in the first place. The security systems will be much stronger when tested with the hacker’s state of mind considered.
The system will ensure that the hacker’s efforts are watered down by countermeasures and an evolving software system that can protect critical assets while moving and backing up information when a hacking attack has been detected.
Cybersecurity is very important for the modern world as the number of hackers is increasing, and the tools that are at their disposal are getting meaner and more lethal. The hackers will always improve their methods, and when they are in a community, they will always be sharing their means and techniques to ensure that they can break into systems more easily.
For instance, hackers have been known to share exploits at a fee to the other hackers targeting specific systems. This will allow them to break into the systems more easily and reduce any complications they might face whenever they are working with information.
Without proper protection, information is exposed to hackers who will not hesitate to lift it and tow it away to the internet’s dark corners. The hackers will also take their time to break encryption keys and other security measures such as passwords.
Businesses and organizations must better understand the methods that they can use to ensure that their information systems are safe and secure from hacking attacks. This will ensure that they can secure themselves, react faster to the jabs of the hackers, and recover much faster without attracting a lot of attention. The customers will put up with half an hour of outage on the business websites and web applications.
However, if the outage gets out of hand, the customers will not be pleased with the business, and most of them will end up going elsewhere. This leads to losses for the business and can be very detrimental to the success of the business. Knowing how best to recover from hacking attacks will ensure companies and businesses can keep rendering services even when they are under heavy attack. A good and effective strategy is required for the modern business to keep operating in a world that seems harsh and hostile to them.
Not many businesses are aware of the threats that are always around them. Whenever they move from traditional systems to digital systems, they do not put security measures to ensure that they are not easily broken into and their information stolen from them. Being aware of cybersecurity threats is one of the most important steps to maintaining a more secure information system for any company or business on the internet.
Securing your business from the many threats around will be very useful and will ensure that your business can survive the many attacks that will no doubt be meted on it. Securing the points of entry for the information system, such as websites and web applications used to log into the information systems, will also be an important part of keeping your information systems secure.
Importance of Information
Information is a very precious asset for any business and organization on the internet, and keeping this information secure is quite important. With information, businesses can render services to their customers, such as handling their orders, giving them useful services, and ensuring that they can conduct transactions on the internet safely and securely.
With the information safe and secure at every step and stage of its processing, it will be possible to keep the business running smoothly. The business will not need to worry about getting intercepted when it has encoded the information from the web application or website where it is being submitted. Without proper security for information systems, hackers will break into these systems with much ease and steal or modify information.
The hackers will always have new methods to try on your information systems, and when you keep your security measures constantly upgraded, you will be sure that nothing will be able to sneak past your firewalls.
Whenever your organization is making changes to the information systems and applications you use, security upgrades to the request form. This will ensure that your data is kept safe at all times. With a secure system, you will not have to worry about the ever-present threat of hackers. The hackers will not be able to easily break into a well-secured system and most of the time.
They will give up after several unsuccessful tries. They will also have a harder time breaking into your system when you have tried to break in like the hacker and patched up the sections that the hacker had a field day breaking into your information system.
Cyber Threats
Cyber threats are very real, and millions of websites are getting infected by malware each second. Up-to-date security standards are a key requirement for your information systems. Whenever you are in the process of upgrading your systems, ensure that firewalls are also upgraded. Maintenance for your defenses is also important and will save you billions in losses that occur due to the hackers breaking into your system and causing damage or stealing the information you have stored in the system.
Hackers are always patient, and when you have automated updates on your software applications, they will always be caught off guard when they try to break into your information systems. The security upgrades will ensure that all the vulnerabilities have been properly patched up. All the hacker will be met with is an upgraded system that does not accept any of their hacking attacks but keeps them locked out of the system.
An evolving security strategy for your information will ensure that you no longer have to worry about hackers getting past your defenses. Instead, all you will be working on is maintaining a powerful defense that will ensure that the hackers cannot get in. keep the hackers out of your information system by learning their ways and adapting to the attacks they attempt on your information systems.
Hackers are known for some very deadly attacks and have caused many systems to come crashing down. They are always resilient and will keep trying all ways and means to get past your unsuspecting firewall. They will also take their time to try as many passwords as possible before they are timed out and locked out of your information system and applications.
Whenever you understand the mindset of the attacker and the vectors they will be most likely to target, then defending your systems will be a lot easier, and you will no longer have to worry about an unprotected portion of your information system or computing infrastructure. It is also important that you learn the security weaknesses present in some of the systems you move to, such as the cloud. Knowing the kind of hacking attacks that can occur on the infrastructure you are migrating to will ensure that you stay more secure and defend yourself from all attacks by the hackers.
Cybersecurity is also very diverse and wide in the number of areas that it covers. For instance, some attacks can only be made on database applications, and others will be done on the networking hardware you use. However, you must understand the danger of hackers and the threat they present to businesses and organizations on the internet.
As people and companies move to the digital front, they must have enough security for their information. Their applications and software will be more secure when they understand the hackers’ methods to use on their applications. Keep your information and software secure from all the attempts of hackers. Patch up your applications regularly, and the hackers will be met with better software the moment they attempt your system.
Conclusion
In this series of blog posts, we will be dedicated to cybersecurity and look at all how an attacker might try to break past your defenses and into your information system. When you understand the hackers and the methods they use to break into your information system, you will be able to relate the hackers’ methods to your everyday experience. As such, you will be able to keep your information secure at all times.
Additionally, you will be a step ahead of the hackers by keeping your applications updated and all your security measures patched up to ensure that you do not present any security weaknesses that the hackers can take advantage of. Hackers are dangerous people and the kind of criminals that will not leave the broken glass on their way out.
Tracking them is usually very hard. When you have proper information systems and security measures in place, it will be possible to trace them or build their profile based on their attack signature and hacking style. So, stay tuned and keep checking back for more hacker tales and cybersecurity adventures.






